For many people who work in cybersecurity, digital forensics, and ethical hacking, having the right tools at the right time can make all the difference. Whether you’re conducting a penetration test, analyzing a compromised...
Read More
How to Perform a Clean Installation of Kali Linux on a Laptop or PC (2025 Guide)
If you’re looking to install the latest version of Kali Linux (2025.1) on your laptop or desktop, you’ve come to the right place. This article walks you through the complete process step by step...
Read More
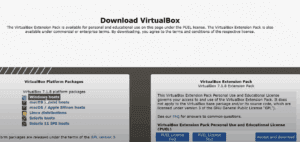
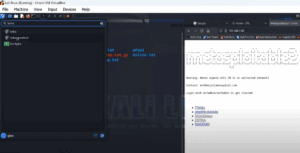
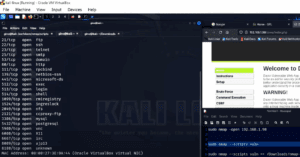
How to Set Up Kali Linux and Metasploitable 2 on VirtualBox (Beginner-Friendly Guide)
Setting up a penetration testing environment on your personal computer is a great way to learn cybersecurity and ethical hacking. This article will walk you through a complete beginner-friendly setup of Kali Linux and...
Read More
How to Download and Install Kali Linux on VMware Workstation (Step-by-Step Guide)
If you’re planning to use Kali Linux for penetration testing or cybersecurity practice, setting it up inside a virtual machine is a smart choice. In this detailed guide, you will learn how to easily...
Read More
Understanding Kali Linux and Its Role in White Hat Hacking
Many of you have often asked me questions about Kali Linux — what it is, and how it is used, especially in the field of ethical hacking.Today, in this article, we’ll dive deep into...
Read More
How to Use Hydra for Brute Force Attacks on Metasploitable Using the CLI
⚠️ Disclaimer: This article is intended for educational purposes and ethical hacking only. Always ensure you have permission before attempting any penetration test. Hydra is one of the most widely used tools for performing...
Read More
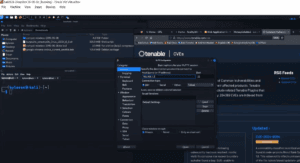
A Step-by-Step Guide to Nmap Vulnerability Scanning Using NSE Scripts
⚠️ Disclaimer: This guide is intended strictly for ethical hacking and penetration testing in controlled environments with explicit permission. Do not attempt this on unauthorized systems. When it comes to penetration testing, simply identifying...
Read More
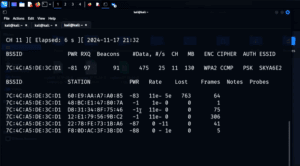
How to Capture and Crack a WPA Handshake Using Aircrack-ng (For Educational Purposes Only)
⚠️ Disclaimer: This technique is intended strictly for educational and ethical penetration testing purposes. It should never be used on public networks or without explicit permission. Always ensure you are working in a controlled...
Read More
What Kind of Person Studies Cybersecurity? Exploring the Tools, Mindset, and Teams That Shape the Field
Cybersecurity is one of the most dynamic and essential fields in today’s digital world. It’s more than just managing firewalls or writing lines of code — it’s about thinking critically, staying curious, and outsmarting...
Read More
Introduction to Shodan: The Search Engine for Internet-Connected Devices
In the world of cybersecurity and ethical hacking, Shodan is an incredibly powerful tool used to identify and analyze devices that are publicly accessible on the internet. From smart homes and business networks to...
Read More
How to Perform Reconnaissance and Vulnerability Testing Using Nikto and Nmap
In the world of cybersecurity and penetration testing, two tools stand out for their usefulness in performing reconnaissance and vulnerability assessments: Nikto and Nmap. Whether you’re a budding ethical hacker or a seasoned IT...
Read More
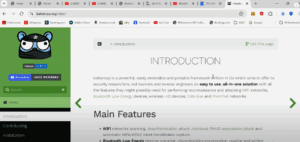
Introduction to BetterCAP: The Swiss Army Knife for Network Penetration Testing
Disclaimer: This article is for educational purposes only. The techniques and tools described should never be used on public networks or without proper authorization. Always ensure your actions comply with applicable laws and ethical...
Read More
How to Test Wi-Fi Security Using Fern WiFi Cracker: A Beginner’s Guide to Ethical Hacking
Disclaimer: This article is intended strictly for educational and ethical hacking purposes. Do not attempt these techniques on any network that you do not own or have explicit permission to test. Unauthorized access to...
Read More